LDAP - How to import users from a remote directory to 2N® Access Commander?
2N® Access Commander can be synchronised with other directories using the LDAP protocol in addition to Active Directory.
This functionality requires a 2N® Access Commander PRO or UNLIMITED license - the license order number is 91379032 (PRO) / 91379033 (UNLIMITED).
Compatible with directories that support the LDAP protocol.
Tested with MS Active Directory, OpenLDAP, Apache DS.
Version 3.0+
How to create a connection to the remote directory
- Log in to your 2N® Access Commander installation.
- Make sure you have the Integration License activated (Settings > Licenses > LDAP synchronization: Yes).
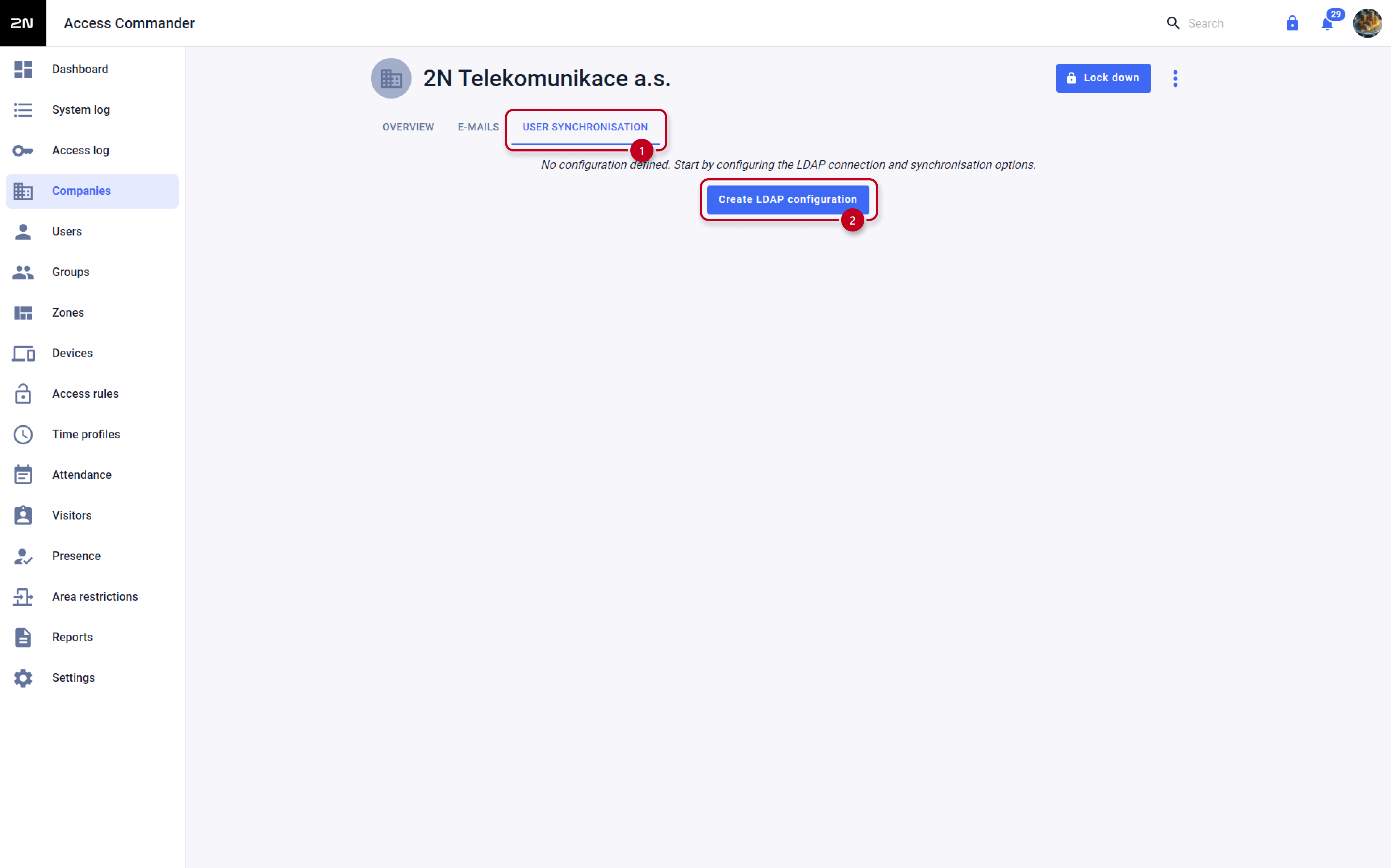
- Open the Companies section and enter the edit of the company to which you want to import users from the given directory:
- In the company settings select the User synchronisation tab and click on CREATE LDAP configuration:
Fill in the Server name, Login name, Password and LDAP Schema and click CREATE at the bottom right:
As an example, the following figure uses the Administrator account (from the directory), which is located in the directory in the container Users
on the acom.local directory domain.
Universal Login name:
CN=<login>,CN=<container_name_in_directory_containing_administrator_with_the_given_login>,DC=<domain>,DC=<domain_suffix>
Just in case of MS Active Directory the input can be: Administrator@acom.local
LDAP Schema (BaseDN):
OU=<organisation_unit_name_in_the_directory_containing_the_users_for_synchronisation>,DC=<domain>,DC=<domain_suffix>
If the users we want to import are deeper in the directory hierarchy, you must fill in the full path. For example, for users who are located in the Sales organisational unit, which is part of the 2N organisational unit, which is already at the root of the directory in the acom.local domain, the schema looks like this:
OU=Sales,OU=2N,DC=acom,DC=local
SSL is not used here - the connection to the server is therefore unsecure.
How to import users from a connected directory, including their contacts and accesses
- After creating a connection to the remote directory, click on Edit schema button:
Here we define the User filter, User name and names of the attributes under which the given information is located in the directory.
In case of MS Active Directory, we can use the already preset User filter "(&(objectclass=user)(objectcategory=person))",
thereby importing only users that have user in the "objectclass" attribute and person in the "objectcategory" attribute.In case of synchronisation from other directories, it is necessary to adjust the filter accordingly to match the requirement of the given directory:
Then confirm by clicking on the CHANGE button.
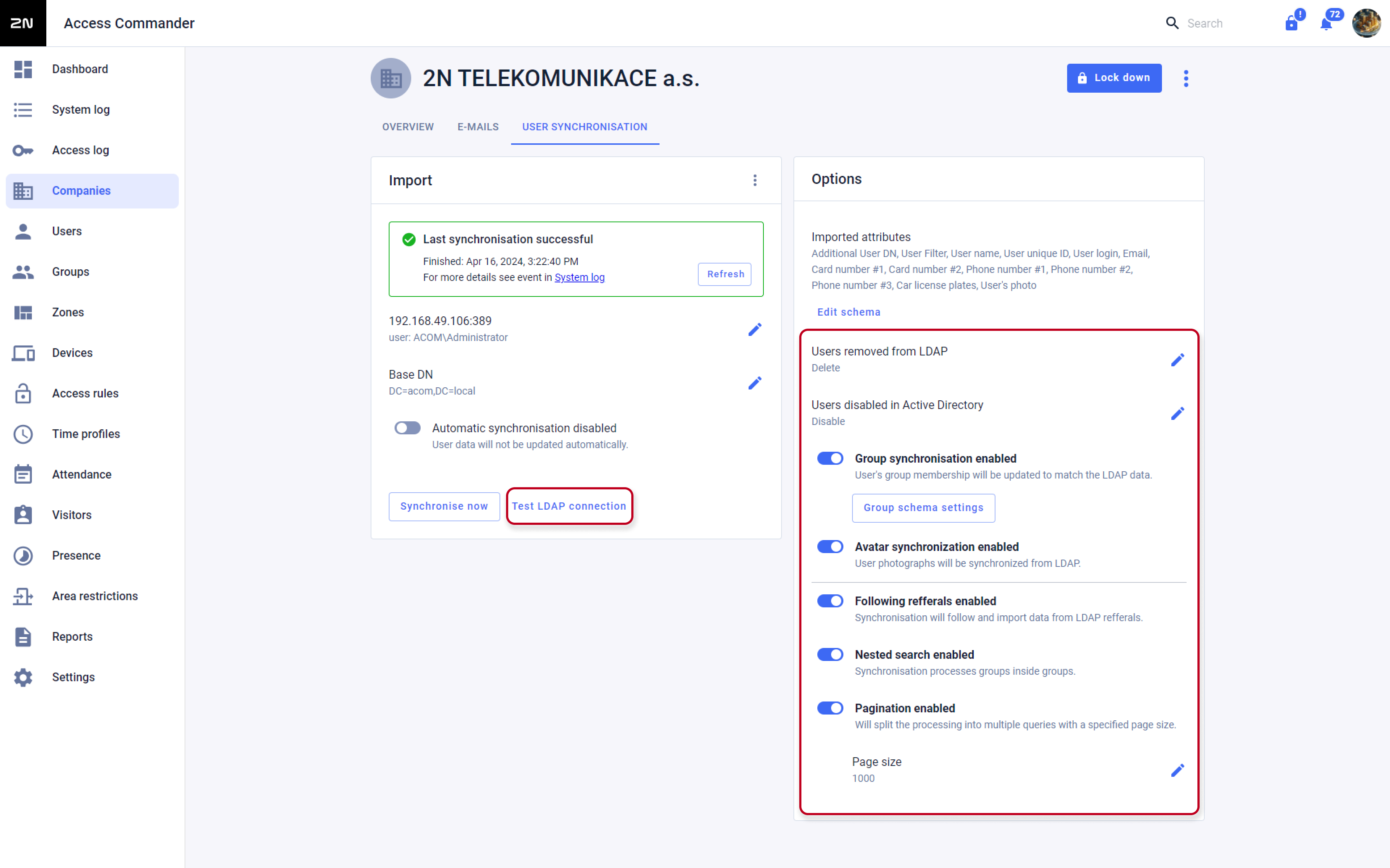
The default User Name ("cn") and attributes below may apply only to MS Active Directory, and in case of synchronisation from other directories, those that differ must be adjusted according to the given directory.Set other parameters of the LDAP synchronisation:
- Nested search: Imports the given users also from subfolders (organisational units or containers) of the selected BaseDN directory.
- Following referrals: Imports the given users from any other repositories of the given directory.
- Avatar synchronisation enabled: If users have a photo assigned to them in the directory, it can also be imported.
- Disable users when disabled in Active Directory: If the user is deactivated in the directory, it will be imported and deactivated in Access Commander
(he won't have access to the door, it won't be able to call him).
- Users removed from LDAP: Choose what Access Commander should do if a user in the given directory is deleted.
Either No Change, or Deactivate, or Delete in Access Commander.
- Pagination: If Access Commander asks the directory for a user, they are sent on so-called pages (to avoid server overload).
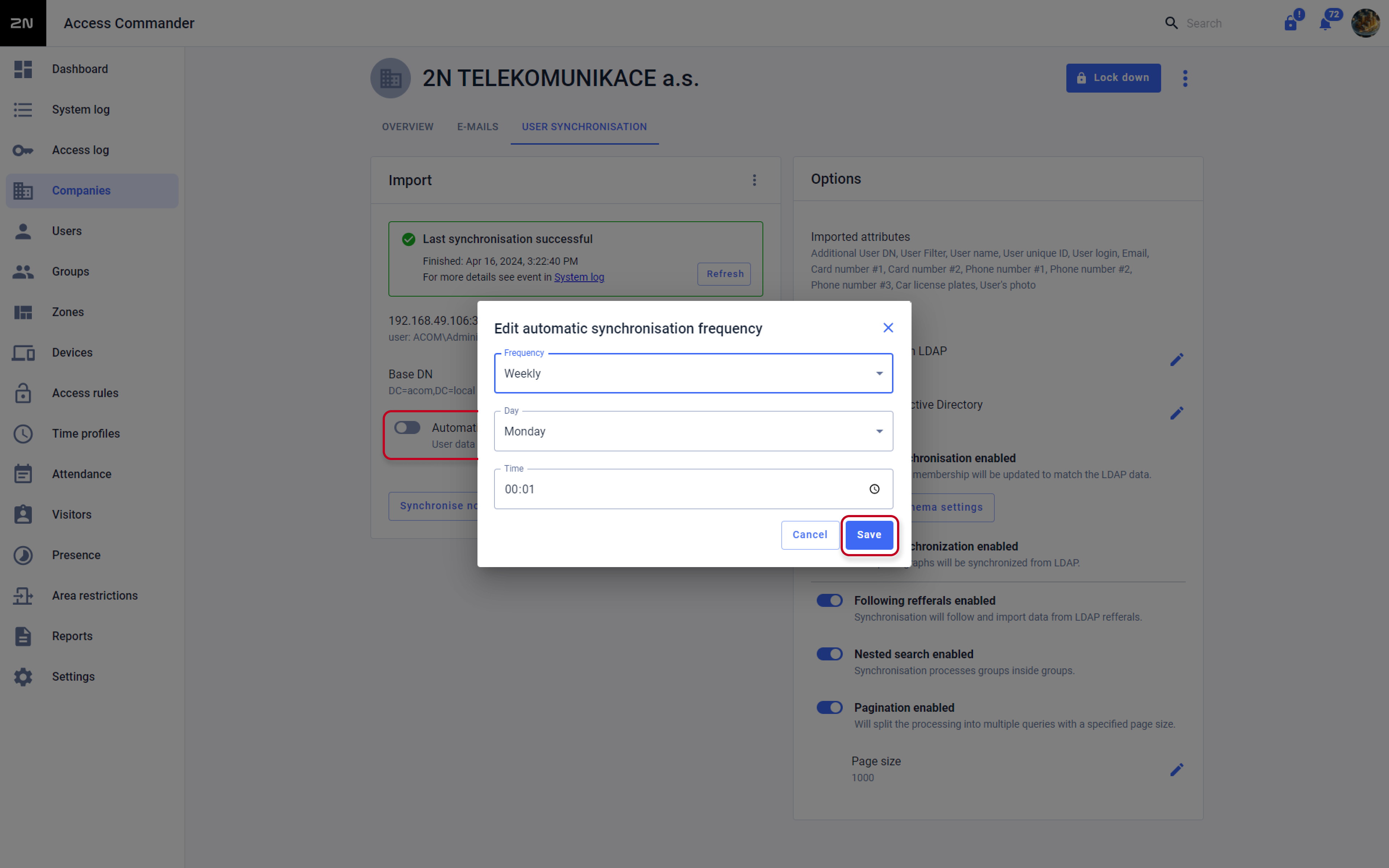
So define here how many users will be sent on one "page" (the value must not exceed the value set in the directory).If you need users from the given directory to be synchronised to 2N® Access Commander automatically,
set the parameter Periodical import time, where we choose between hourly, daily and weekly intervals,
select the minute, hour or day of the regular synchronisation and confirm by clicking on the CHANGE button:Finally, you can validate the LDAP configuration by clicking on the appropriate button below
and by clicking the IMPORT button (above left) information about users from the given directory will be downloaded to the 2N® Access Commander (see the picture below).
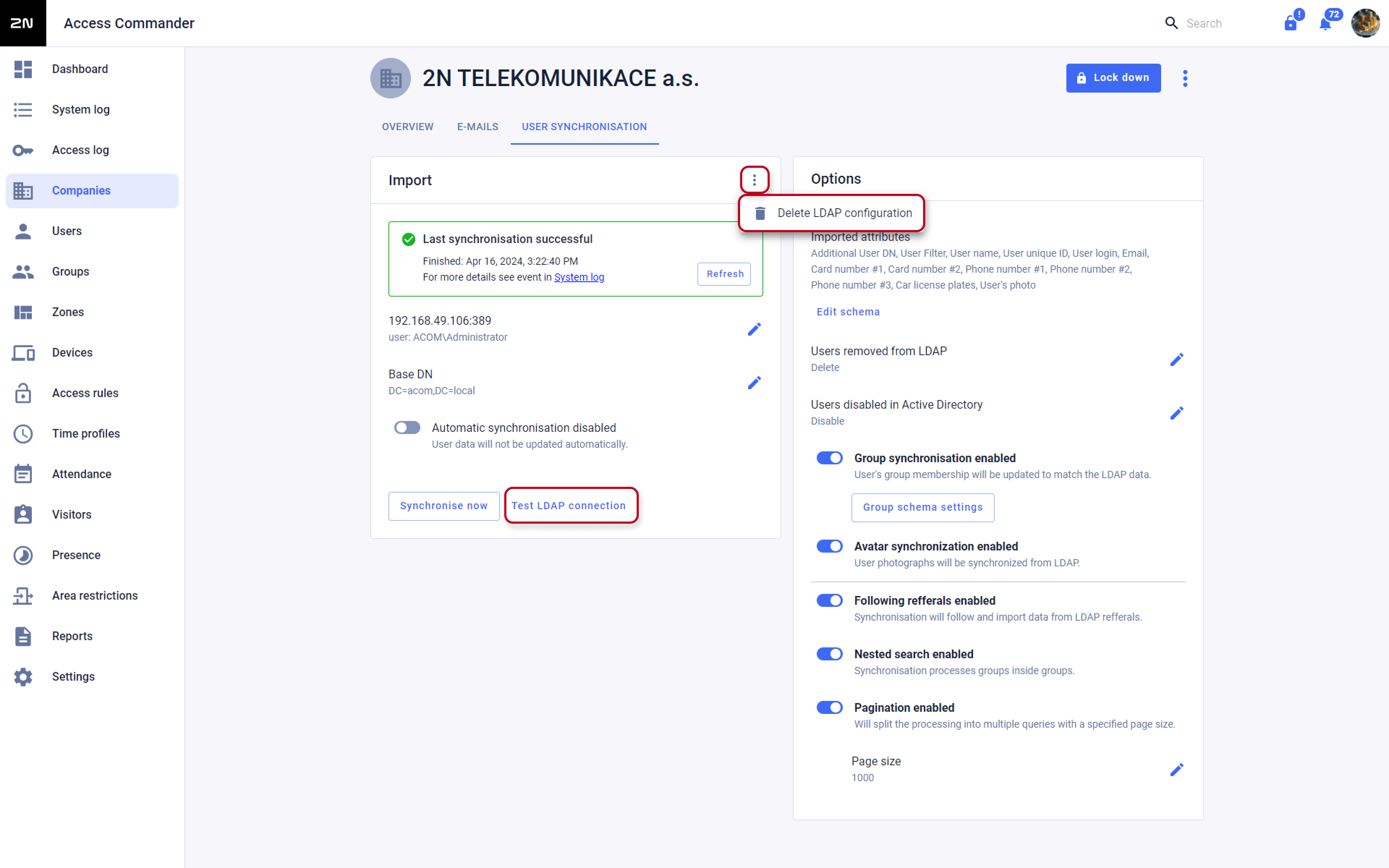
You can find the imported users in the Users section under the given Company in the 2N® Access Commander.In the import section you can see the Last import status and you can completely delete the LDAP synchronisation with the DELETE LDAP CONFIGURATION button when showing more option of the Import sectiont.
How to import an RFID card identifier or PIN code with the user
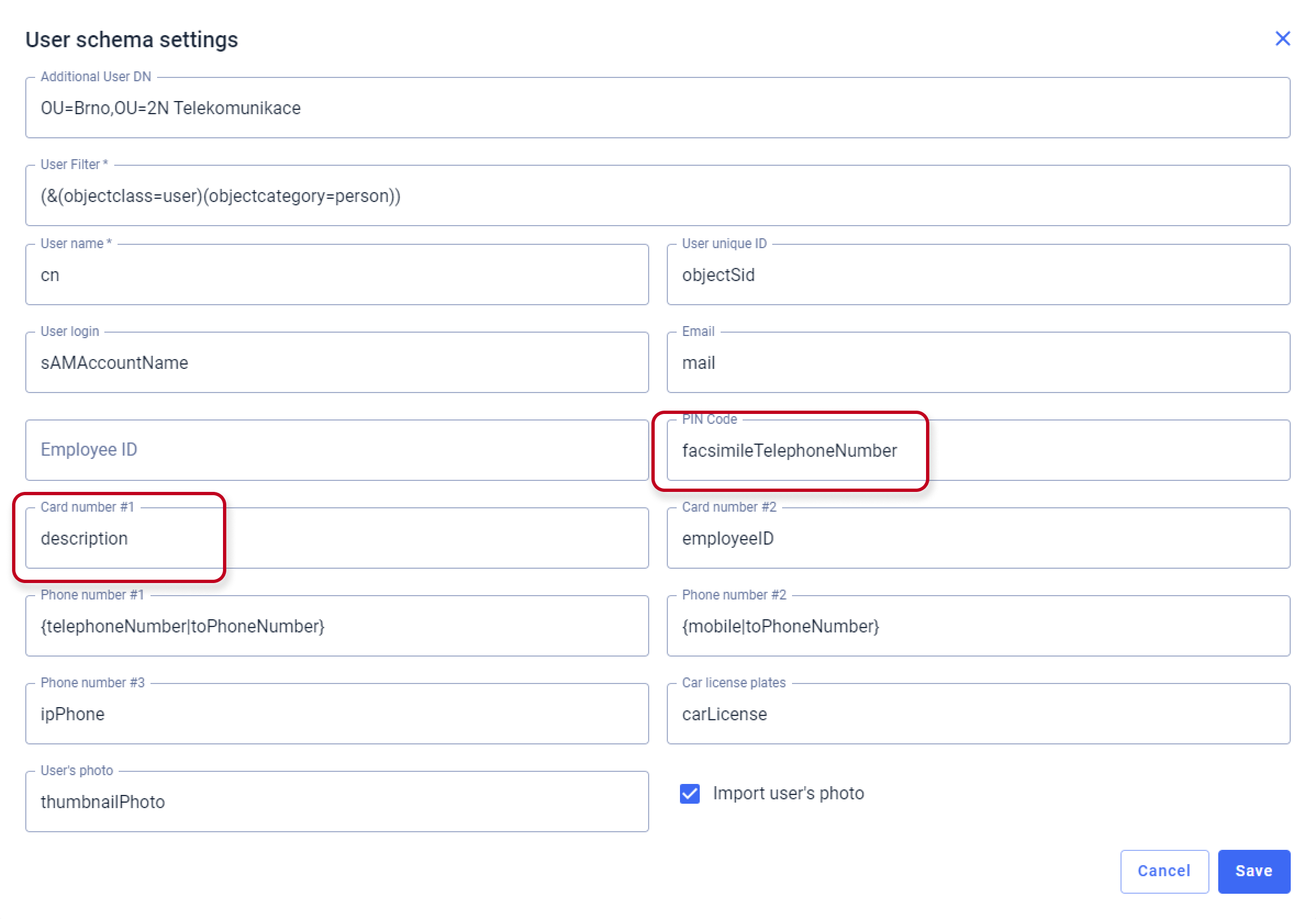
- Click on the Edit schema option:
Here we define the names of the attributes in the directory from which the individual information is downloaded. In the case of cards or PIN codes, we often have to use the box for another item, as there is usually no space in the directory for a card identifier or PIN code.
The following example shows that for the identifier of card 1 we used the Description field in the directory and for the PIN code the Fax field in the user detail.
Therefore, in order to be able to import the given information, it is necessary to set up 2N® Access Commander to search for this information in the given user's detail fields in the directory:The names of the individual attributes (for MS Active Directory) are then described here: https://docs.classic.secureauth.com/display/KBA/Active+Directory+Attributes+List)
Example:
PIN Code we entered for example into the "Fax" field in the directory - the name of this attribute in the directory is: facsimileTelephoneNumber
Card Number #1we entered for example into the "Description" field in the directory - the name of this attribute in the directory is:description
For the second card a separate field must be selected in the user's detail.
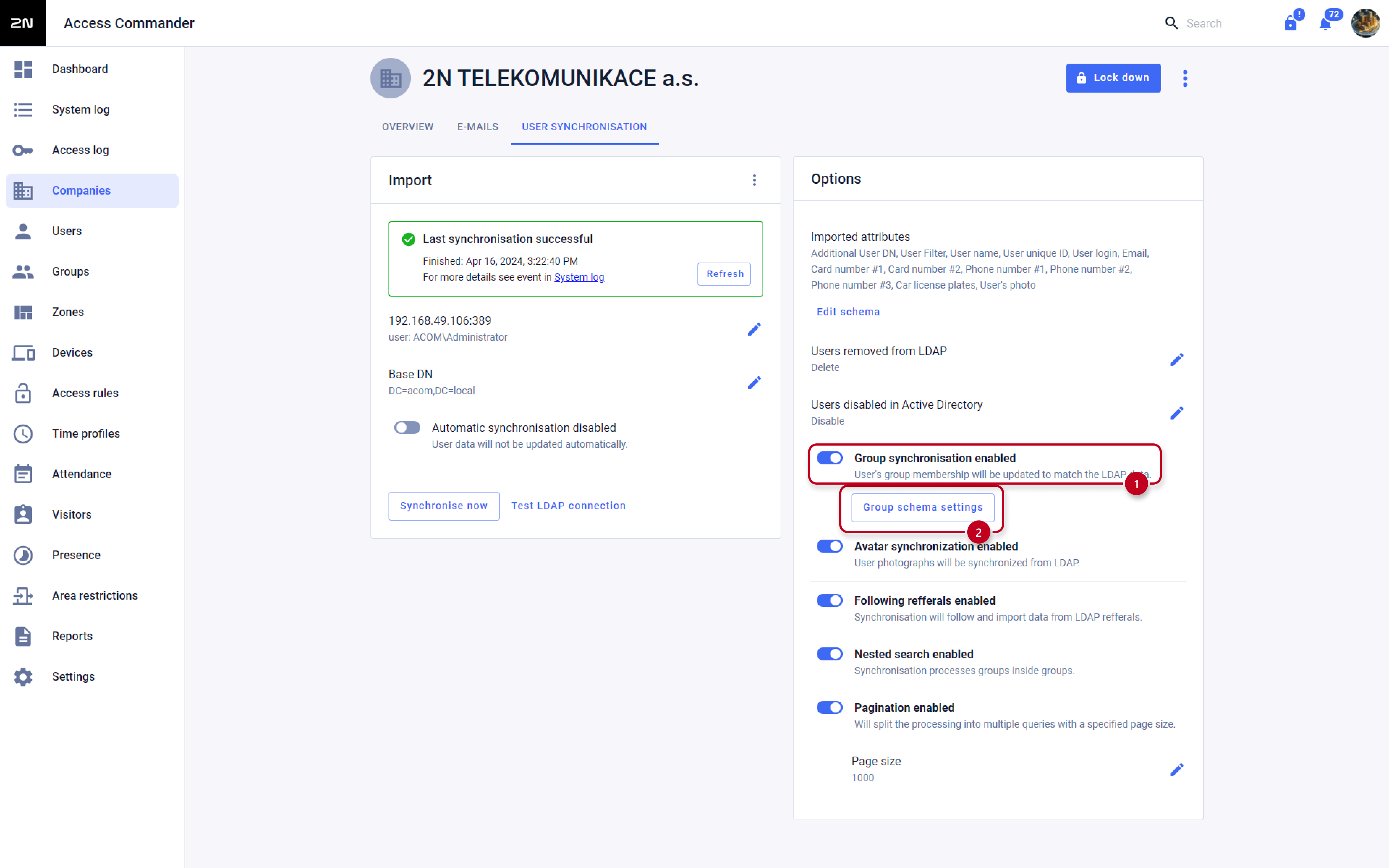
How to synchronize group membership for imported users
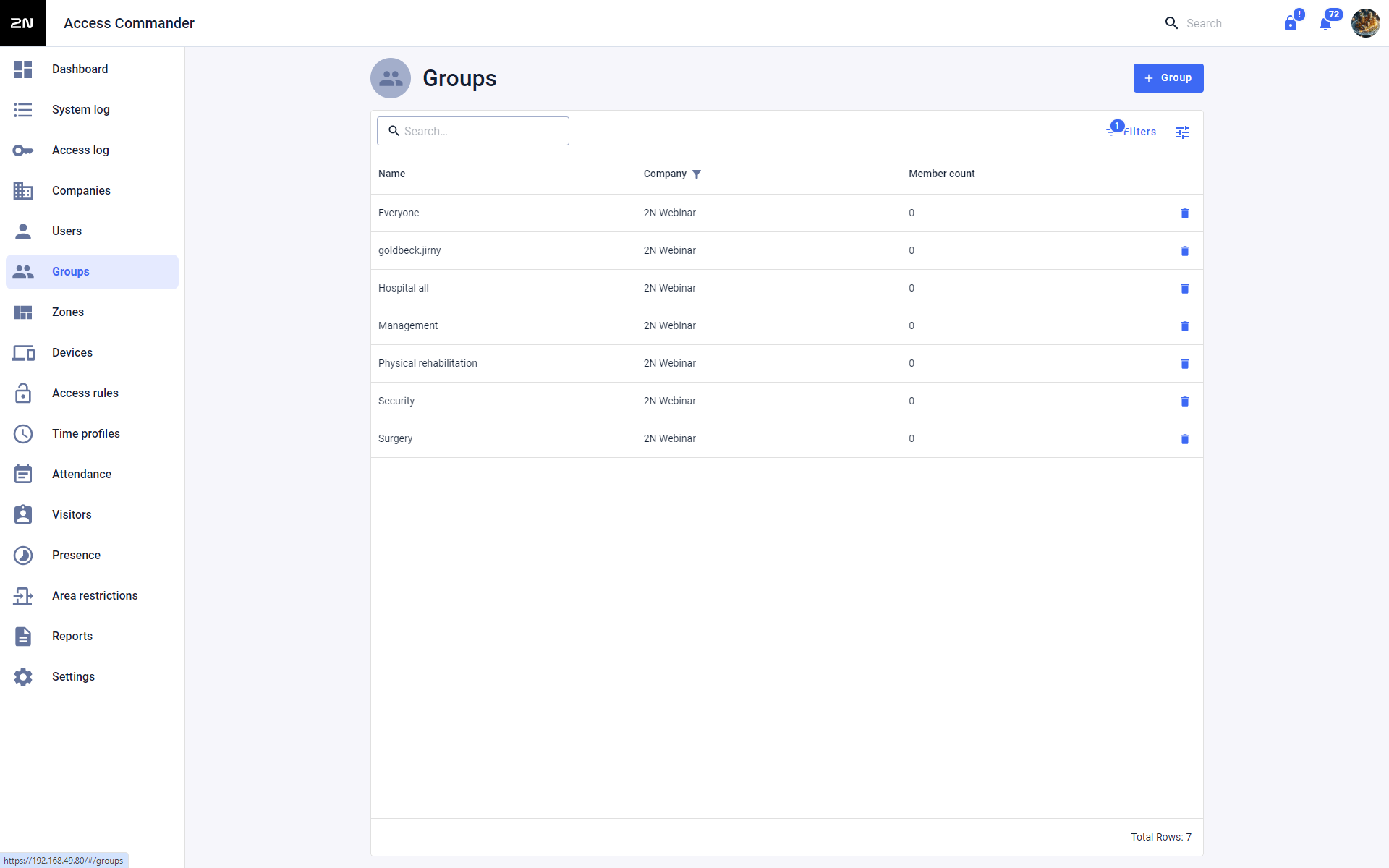
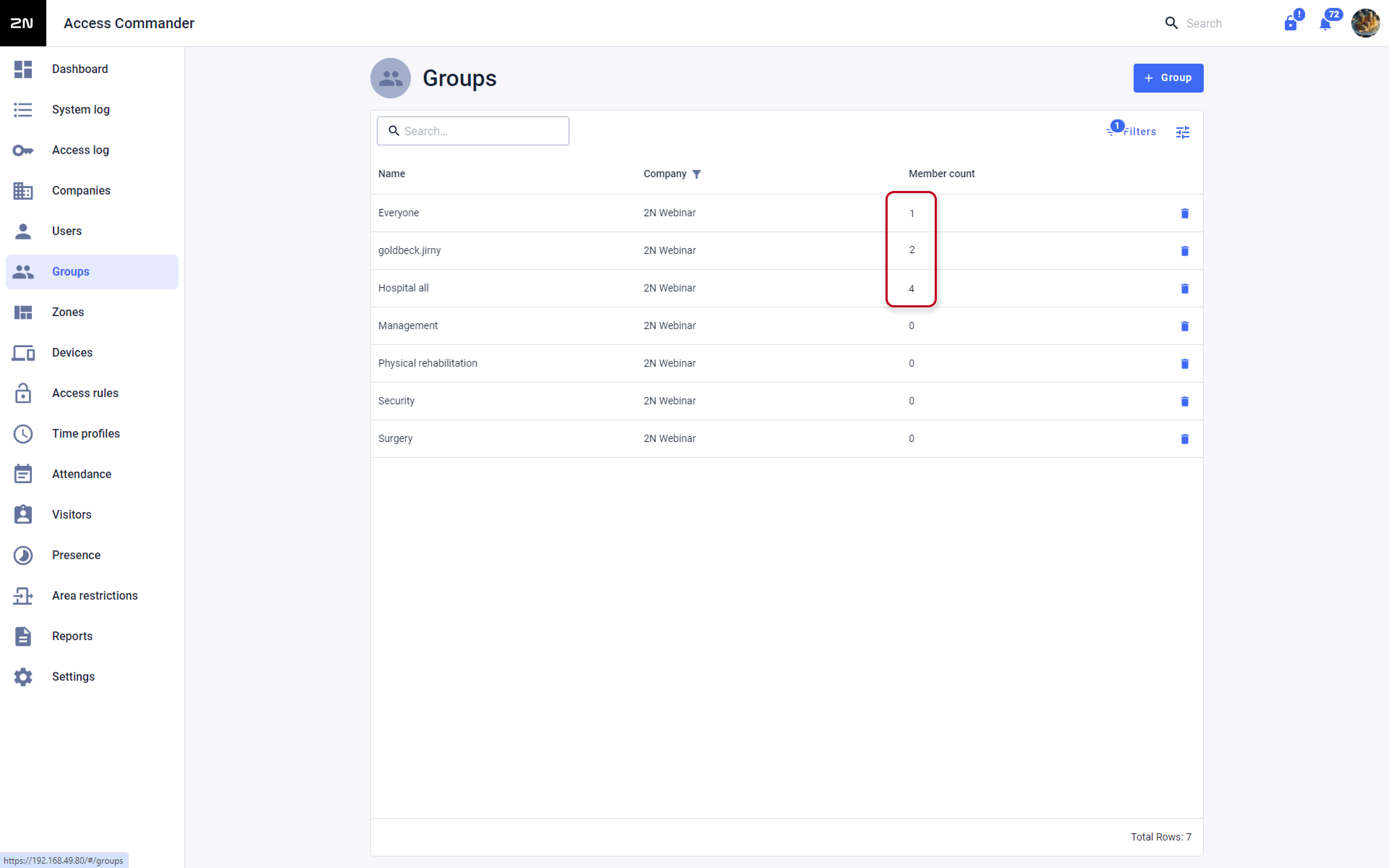
Please be informed, that this is not an import of the groups from the LDAP directory, this is only a Synchronization of the membership, you need to manually create those groups in your Access Commander database. This was done to prevent importing all unnecessary groups, that are not tied with accesses of the users (e-mail groups etc.)
- If you have done all of the steps above, you now should have users in your database with their accesses, phone numbers etc.
Now you can create groups in the Access Commander, keep in mind that the name of the group is case sensitive and must be exactly the same as you use in your remote directory.
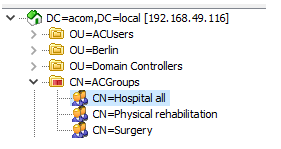
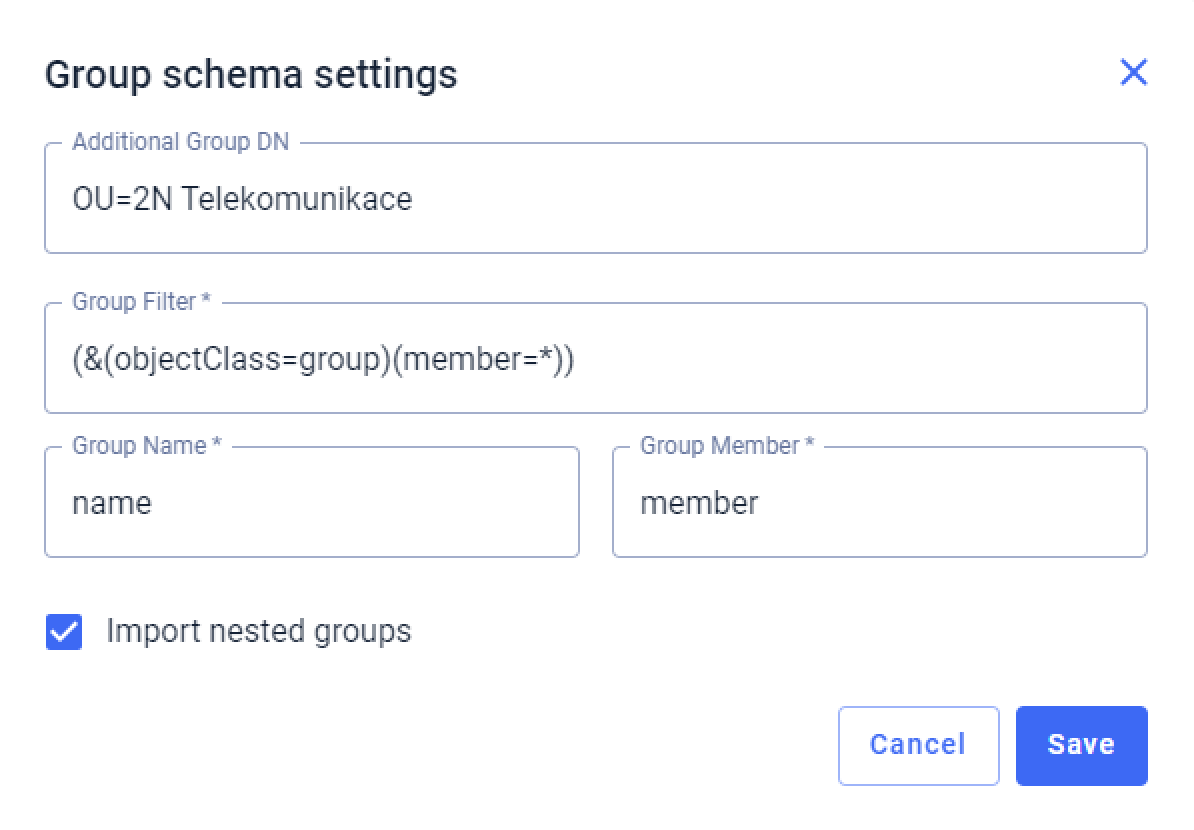
After you create all the necessary groups, you need to enable synchronization in the Access Commander and edit group schema settings according to your needs
Additional Group DN:
CN=<container_name_in_directory_containing_groups_of_users>
(do not insert BaseDN as it will be automatically used according to the LDAP schema set in previous steps)
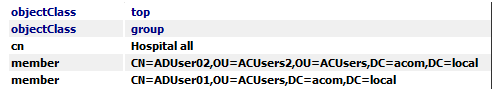
Group Filter:
In our example, we used a filter for MS Active Directory (&(objectClass=group)(member=*)), thereby synchronizing the users with groups that have "group" in the "objectclass" attribute and "member" in the "objectcategory" attribute and they are also simultaneously created in the Access Commander.
The default Group Name ("cn") and Group Member ("member") above may apply only to MS Active Directory, and in case of synchronisation from other directories, those that differ must be adjusted according to the given directory.Now you can import the LDAP settings and check if everything is properly synchronized and the users are assigned to the correct groups
Version 2.7 or older
How to create a connection to the remote directory
- Log in to your 2N® Access Commander installation.
- Make sure you have the Integration License activated (Settings > Licenses > LDAP synchronization: Yes).
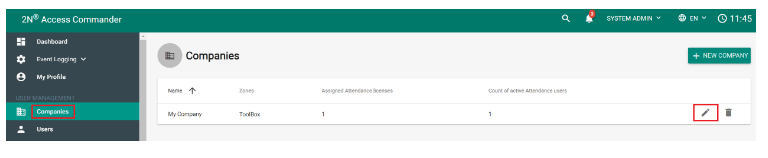
- Open the Companies section and enter the edit of the company to which you want to import users from the given directory:
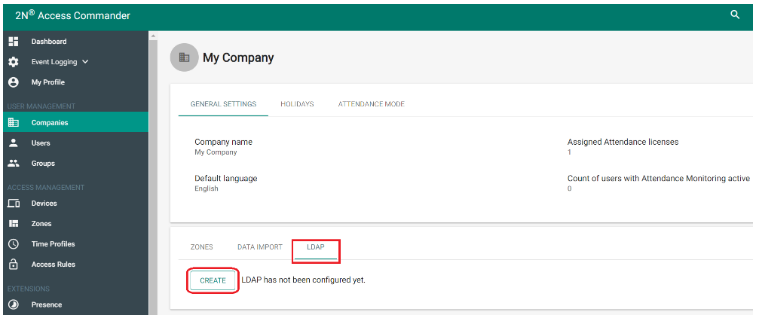
- In the company settings select the LDAP tab and click on CREATE (LDAP configuration):
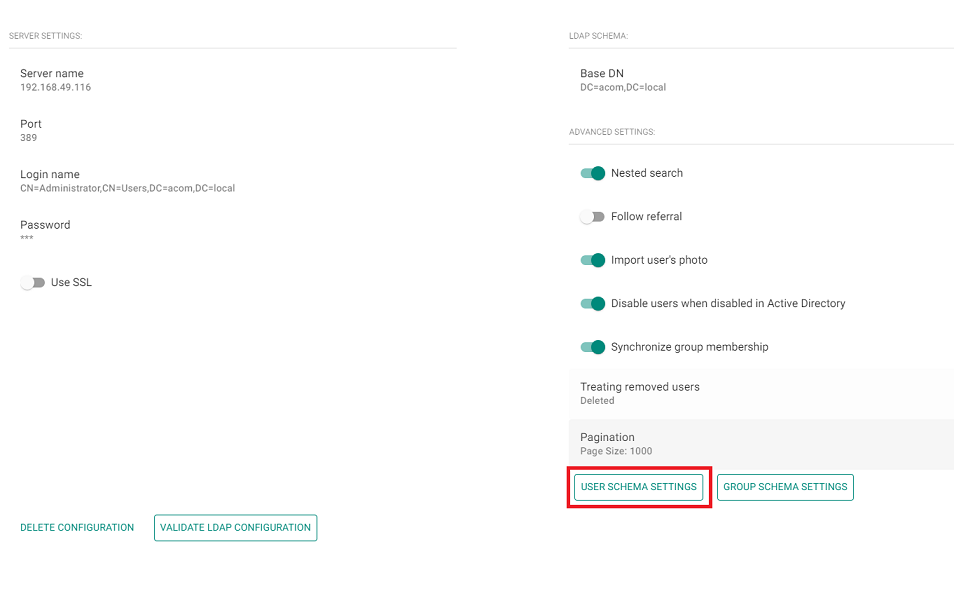
Fill in the Server name, Login name, Password and LDAP Schema and click CREATE at the bottom right:
As an example, the following figure uses the Administrator account (from the directory), which is located in the directory in the container Users
on the acom.local directory domain.
Universal Login name:
CN=<login>,CN=<container_name_in_directory_containing_administrator_with_the_given_login>,DC=<domain>,DC=<domain_suffix>
Just in case of MS Active Directory the input can be: Administrator@acom.local
LDAP Schema (BaseDN):
OU=<organisation_unit_name_in_the_directory_containing_the_users_for_synchronisation>,DC=<domain>,DC=<domain_suffix>
If the users we want to import are deeper in the directory hierarchy, you must fill in the full path. For example, for users who are located in the Sales organisational unit, which is part of the 2N organisational unit, which is already at the root of the directory in the acom.local domain, the schema looks like this:
OU=Sales,OU=2N,DC=acom,DC=local
SSL is not used here - the connection to the server is therefore unsecure.
How to import users from a connected directory, including their contacts and accesses
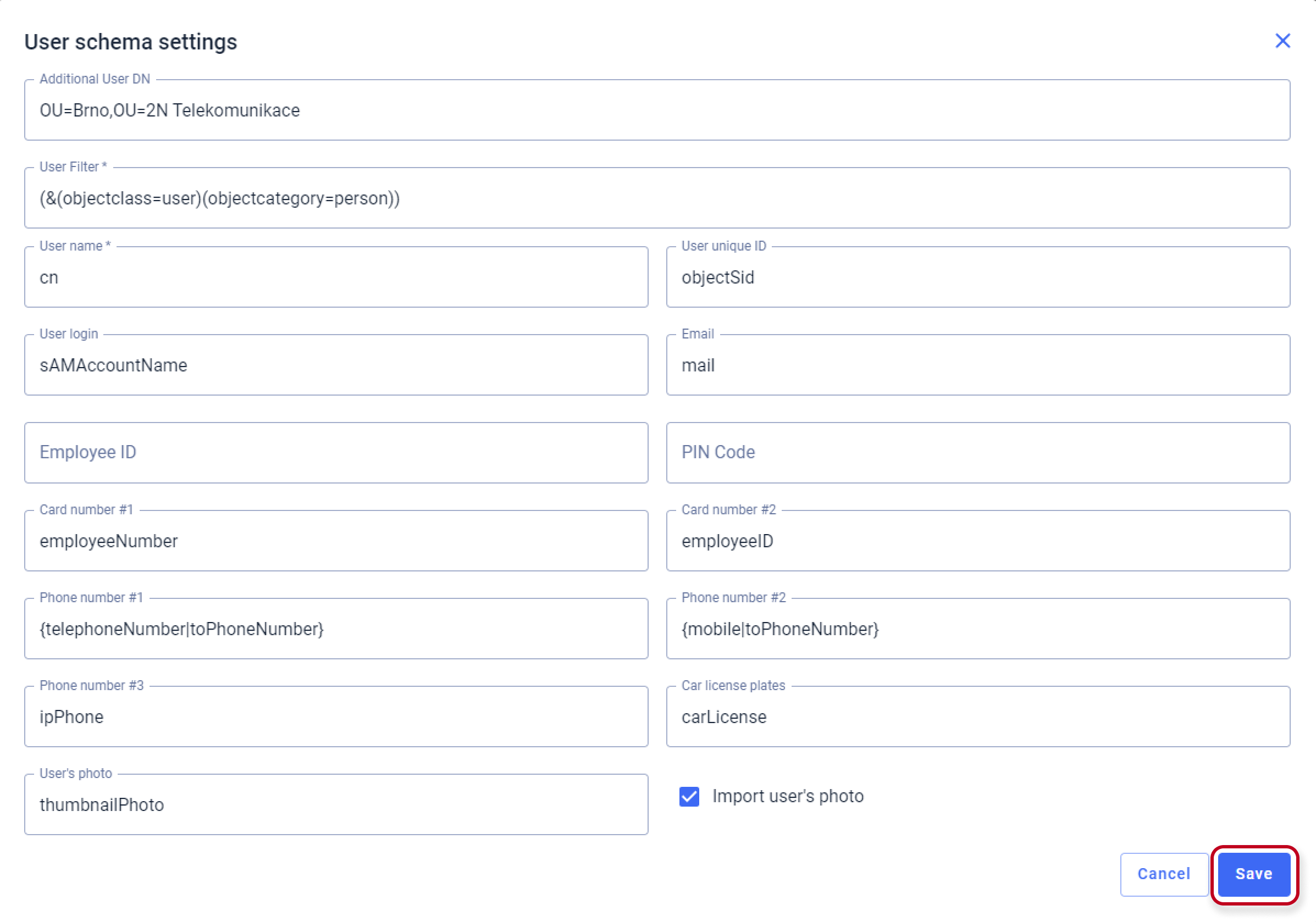
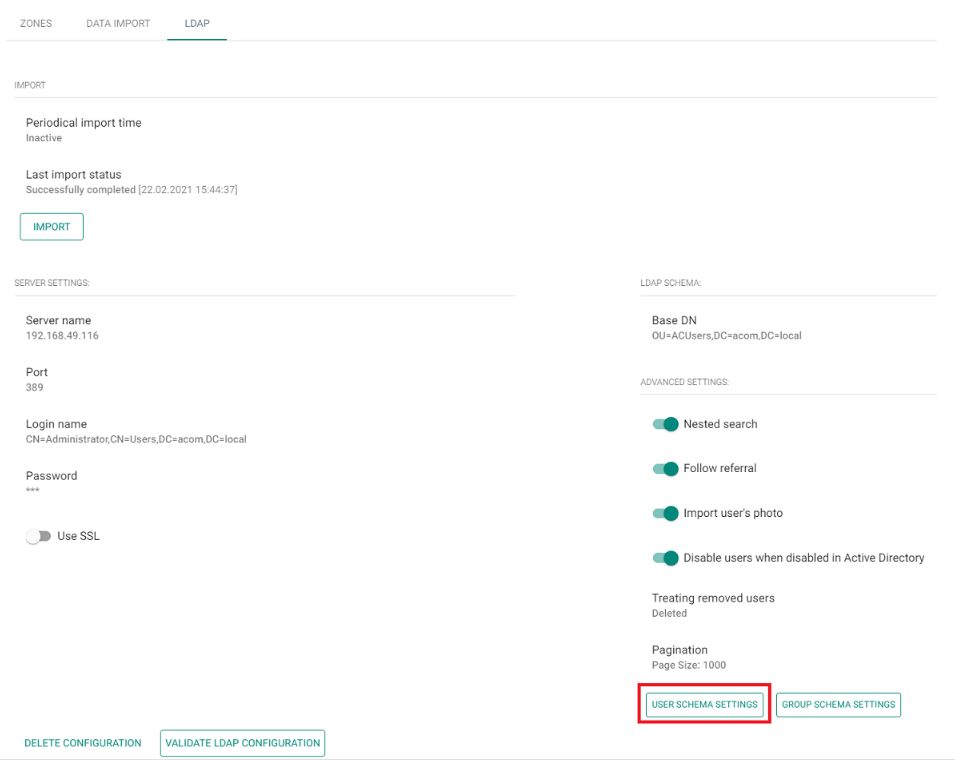
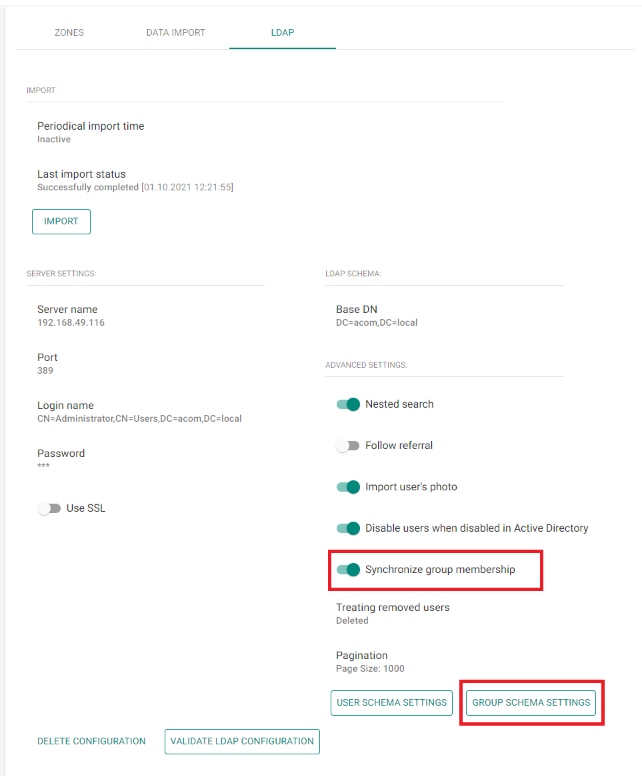
- After creating a connection to the remote directory, click the USER SCHEMA SETTINGS button:
Here we define the User filter, User name and names of the attributes under which the given information is located in the directory.
In case of MS Active Directory, we can use the already preset User filter "(&(objectclass=user)(objectcategory=person))",
thereby importing only users that have user in the "objectclass" attribute and person in the "objectcategory" attribute.In case of synchronisation from other directories, it is necessary to adjust the filter accordingly to match the requirement of the given directory:
The default User Name ("cn") and attributes below may apply only to MS Active Directory, and in case of synchronisation from other directories, those that differ must be adjusted according to the given directory.
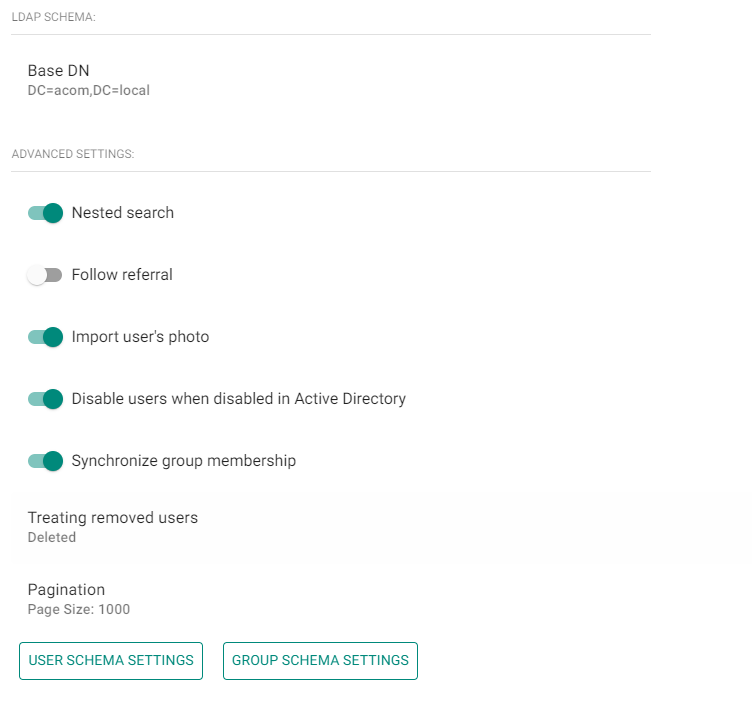
Then confirm by clicking on the CHANGE button.Set other parameters of the LDAP synchronisation:
- Nested search: Imports the given users also from subfolders (organisational units or containers) of the selected BaseDN directory.
- Follow referral: Imports the given users from any other repositories of the given directory.
- Import user's photo: If users have a photo assigned to them in the directory, it can also be imported.
- Disable users when disabled in Active Directory: If the user is deactivated in the directory, it will be imported and deactivated in Access Commander
(he won't have access to the door, it won't be able to call him).
- Treating removed users: Choose what Access Commander should do if a user in the given directory is deleted.
Either No Change, or Deactivate, or Delete in Access Commander.
- Pagination: If Access Commander asks the directory for a user, they are sent on so-called pages (to avoid server overload).
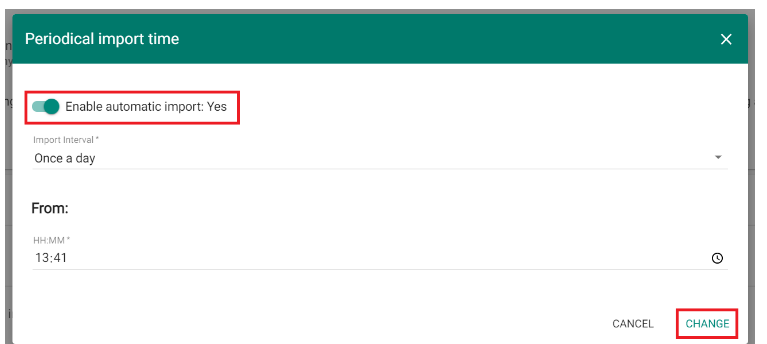
So define here how many users will be sent on one "page" (the value must not exceed the value set in the directory).If you need users from the given directory to be synchronised to 2N® Access Commander automatically,
set the parameter Periodical import time, where we choose between hourly, daily and weekly intervals,
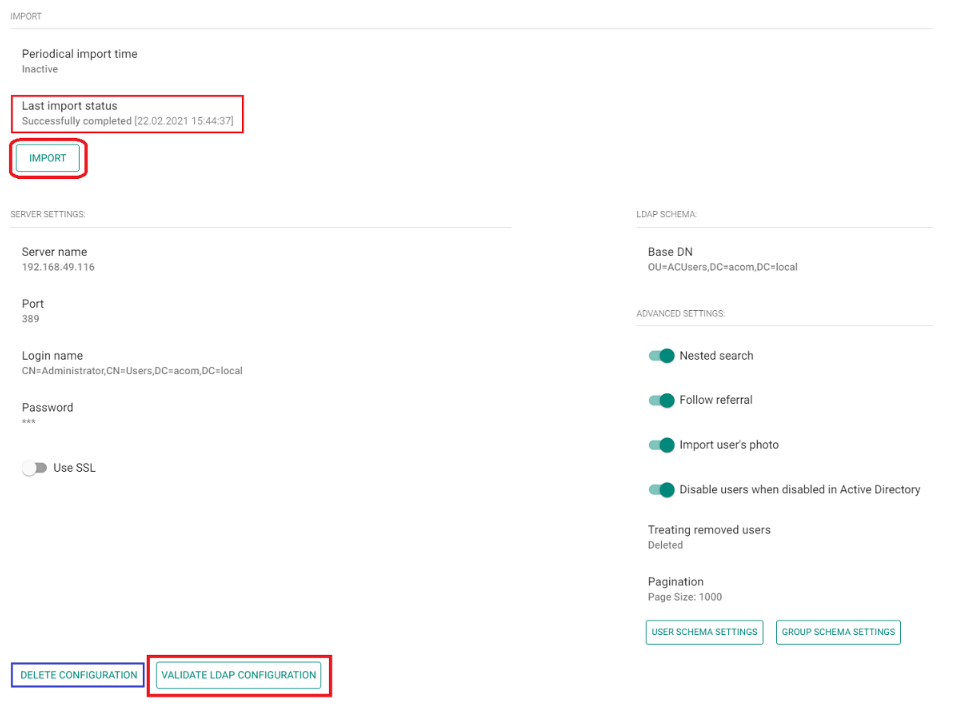
select the minute, hour or day of the regular synchronisation and confirm by clicking on the CHANGE button:Finally, you can validate the LDAP configuration by clicking on the appropriate button below
and by clicking the IMPORT button (above left) information about users from the given directory will be downloaded to the 2N® Access Commander (see the picture below).
You can find the imported users in the Users section under the given Company in the 2N® Access Commander.At the top left you can check the Last import status under the appropriate field
and you can completely delete the LDAP synchronisation with the DELETE CONFIGURATION button at the bottom left.
How to import an RFID card identifier or PIN code with the user
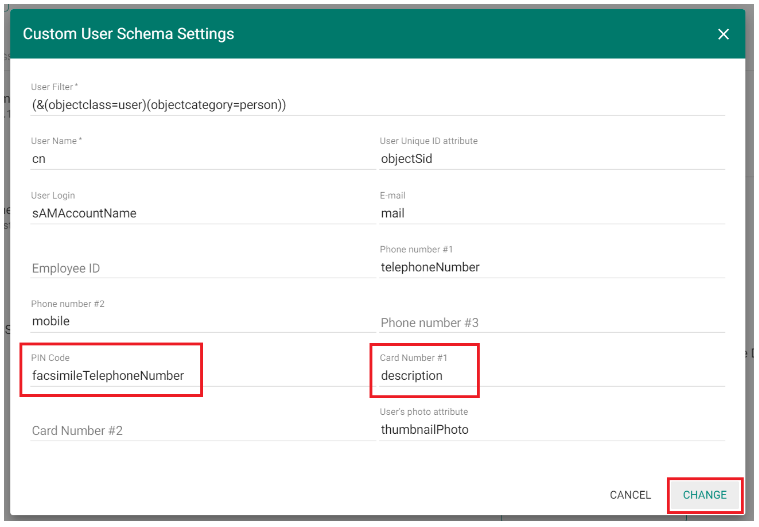
- Click the USER SCHEMA SETTINGS button:
Here we define the names of the attributes in the directory from which the individual information is downloaded. In the case of cards or PIN codes, we often have to use the box for another item, as there is usually no space in the directory for a card identifier or PIN code.
The following example shows that for the identifier of card 1 we used the Description field in the directory and for the PIN code the Fax field in the user detail.
Therefore, in order to be able to import the given information, it is necessary to set up 2N® Access Commander to search for this information in the given user's detail fields in the directory:The names of the individual attributes (for MS Active Directory) are then described here: https://docs.classic.secureauth.com/display/KBA/Active+Directory+Attributes+List)
Example:
PIN Code we entered for example into the "Fax" field in the directory - the name of this attribute in the directory is: facsimileTelephoneNumber
Card Number #1we entered for example into the "Description" field in the directory - the name of this attribute in the directory is:description
For the second card a separate field must be selected in the user's detail.
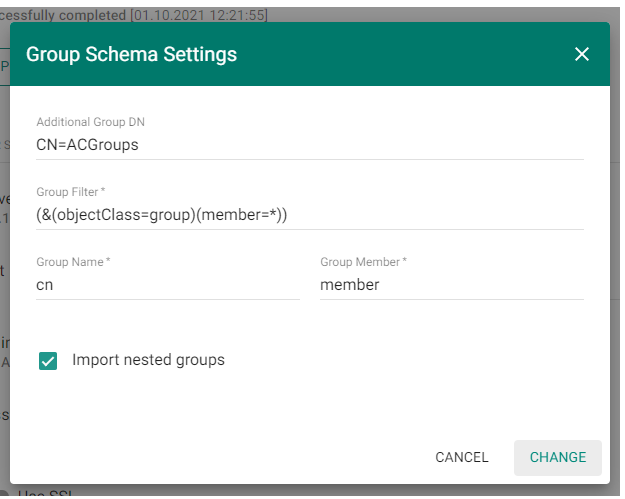
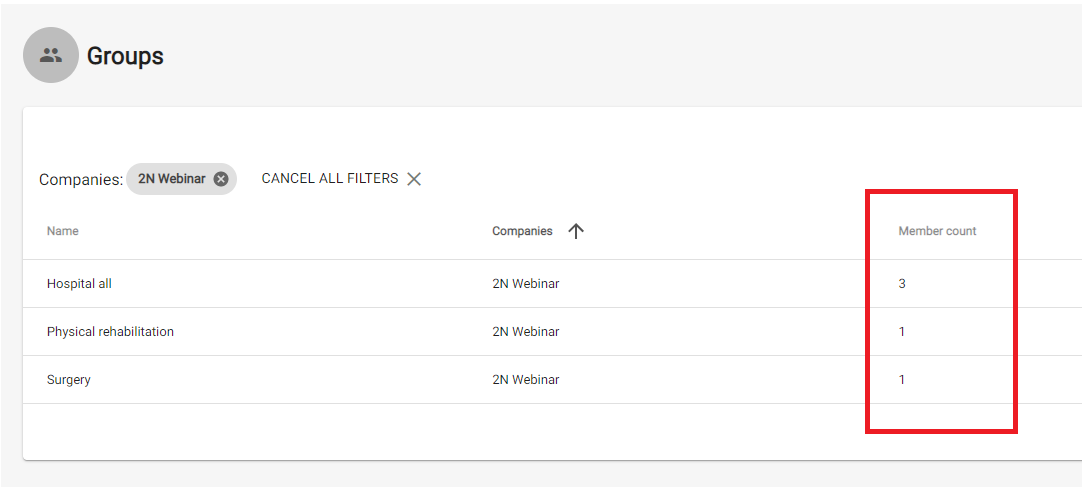
How to synchronize group membership for imported users
Please be informed, that this is not an import of the groups from the LDAP directory, this is only a Synchronization of the membership, you need to manually create those groups in your Access Commander database. This was done to prevent importing all unnecessary groups, that are not tied with accesses of the users (e-mail groups etc.)
- If you have done all of the steps above, you now should have users in your database with their accesses, phone numbers etc.
Now you can create groups in the Access Commander, keep in mind that the name of the group is case sensitive and must be exactly the same as you use in your remote directory.
After you create all the necessary groups, you need to enable synchronization in the Access Commander and edit group schema settings according to your needs
Additional Group DN:
CN=<container_name_in_directory_containing_groups_of_users>
(do not insert BaseDN as it will be automatically used according to the LDAP schema set in previous steps)
Group Filter:
In our example, we used a filter for MS Active Directory (&(objectClass=group)(member=*)), thereby synchronizing the users with groups that have "group" in the "objectclass" attribute and "member" in the "objectcategory" attribute and they are also simultaneously created in the Access Commander.
The default Group Name ("cn") and Group Member ("member") above may apply only to MS Active Directory, and in case of synchronisation from other directories, those that differ must be adjusted according to the given directory.Now you can import the LDAP settings and check if everything is properly synchronized and the users are assigned to the correct groups